Search Results:
Dns encryption standards
posted on 02 Mar 2026 under category security
Post Meta-Data
| Date | Language | Author | Description |
|---|---|---|---|
| 02.03.2026 | English | Claus Prüfer (Chief Prüfer) | An Insight Into Current DNS Encryption Standards |
An Insight Into Current DNS Encryption Standards



The Domain Name System (DNS) stands as one of the internet’s most critical yet persistently vulnerable infrastructure components. Despite decades of evolution and numerous encryption initiatives, the DNS ecosystem has devolved into a fragmented, complex landscape where multiple subsystems compete, overlap, and often undermine each other’s security objectives. The original promise of securing DNS queries—protecting both caching name servers (CNS) and authoritative name servers (ANS)—remains frustratingly distant from universal implementation.
This article examines the current DNS mess, dissects the layers of complexity that prevent simple, global DNS encryption, and proposes a pragmatic path forward for achieving comprehensive DNS security.
DNS Subtypes
The Domain Name System was first formalized by Paul Mockapetris in 1983 under RFC 882 and RFC 883, with the canonical specification subsequently consolidated in RFC 1034 and RFC 1035. The protocol operates in plaintext over UDP port 53, with transparent fallback to TCP for responses exceeding 512 bytes; it carries no inherent confidentiality, integrity, or authentication mechanisms, rendering every query and response fully legible to any on-path observer. Recognizing this systemic exposure, the networking community initiated the first substantive encryption efforts in the late 1990s, leading to the publication of the DNS Security Extensions (DNSSEC) framework in 2005 and, a decade later, to transport-layer encryption standards DNS-over-TLS (2016) and DNS-over-HTTPS (2018).
The client resolver configuration resides in /etc/resolv.conf, which accepts multiple nameserver directives listing fallback resolvers in order of preference. At the infrastructure level, DNS is inherently scalable: public resolvers such as Cloudflare (1.1.1.1) and Google (8.8.8.8) deploy their endpoints behind anycast IP addresses, routing each query to the topologically nearest instance without any client-side reconfiguration.
ANS - Authoritative
An Authoritative Name Server (ANS) holds the canonical zone data for one or more DNS domains and responds to queries from recursive resolvers with authoritative answers—indicated by the Authoritative Answer (AA) flag—drawing exclusively from locally provisioned resource records rather than any cache. It constitutes the definitive source of truth for a delegated zone and is deployed at the apex of each domain’s DNS delegation hierarchy. Principal software implementations include ISC BIND, PowerDNS Authoritative Server, NSD (Name Server Daemon), Knot DNS, Nominum DNS, and dnsmasq operating in its authoritative mode, each offering varying trade-offs in performance, feature completeness, and operational complexity.
CNS - Caching
A Caching Name Server (CNS), also referred to as a recursive resolver, fulfills client DNS requests by traversing the DNS hierarchy from the root zone downwards, querying authoritative servers at each delegation boundary until a definitive answer is obtained. The resolver caches responses for the duration prescribed by each resource record’s Time-to-Live (TTL) value, thereby reducing query latency and upstream load on authoritative infrastructure for subsequent identical requests. Widely deployed implementations include ISC BIND in recursive mode, Unbound, PowerDNS Recursor, and dnsmasq, the latter being commonly embedded in home gateway appliances and enterprise edge devices.
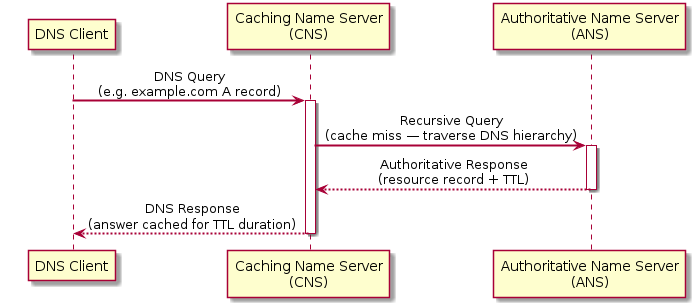
CNS - ANS Workflow Diagram
The standard DNS resolution sequence proceeds through four well-defined stages: the client dispatches a recursive query to its configured CNS; the CNS, absent a valid cached entry, traverses the DNS hierarchy from a root name server through the applicable TLD name servers until the responsible ANS is identified; the ANS returns an authoritative response to the CNS; and the CNS, having cached the answer for the TTL-prescribed duration, delivers the final response to the originating client.
Current DNS Encryption Protocols
As of 2008—when the Kaminsky DNS cache poisoning vulnerability demonstrated the systemic fragility of unauthenticated, plaintext DNS at scale—the urgency to retrofit cryptographic protections into the DNS protocol hierarchy intensified substantially, catalyzing accelerated standardization of the encryption protocols described below. The attack surface extends beyond cache poisoning alone: because DNS operates over plaintext UDP, any on-path attacker is positioned to intercept, inspect, and modify both queries and responses (man-in-the-middle transport attack). The severity of this threat is compounded significantly when combined with ARP spoofing, which allows an attacker on the same Layer 2 segment to silently redirect all DNS traffic through an adversary-controlled host—enabling credential harvesting, traffic redirection, and targeted phishing at scale without requiring any compromise of the DNS infrastructure itself.
DNSSEC - DNS Security Extensions
DNS Security Extensions (DNSSEC), standardized in RFC 4033–4035 (2005), introduce cryptographic signing of DNS resource record sets through a public-key infrastructure anchored at the DNS root zone, which was itself signed in 2010. Zone administrators sign their zone data with asymmetric key pairs (RRSIG records), and validating resolvers verify the chain of signatures from the root through each TLD delegation to the target zone via a hierarchy of DNSKEY and DS records, providing both data-origin authentication and integrity verification.
DNSSEC is applicable to both ANS and CNS roles: Authoritative Name Servers perform zone signing and publish the associated key material, while Caching Name Servers configured with DNSSEC validation verify the cryptographic chain on behalf of clients. Crucially, DNSSEC does not encrypt query or response payloads—queries remain visible to on-path observers—and its deployment complexity, particularly the management of key rollover procedures, has led to notoriously low zone-signing adoption rates despite nearly two decades of standardization.
DoH - DNS-over-HTTPS
DNS-over-HTTPS (DoH), specified in RFC 8484 (2018), encapsulates DNS wire-format messages within standard HTTPS requests transmitted over TCP port 443, rendering DNS traffic indistinguishable from ordinary web traffic and thereby providing transport-layer confidentiality through the underlying TLS session as well as resistance to passive eavesdropping and active interference. The protocol authenticates the resolver endpoint via standard X.509 certificates and supports both GET and POST HTTP methods for query transmission.
DoH is principally applicable to the communication segment between DNS clients and their designated Caching Name Server; it is not designed for CNS-to-ANS recursive resolution traffic, and ANS-side DoH deployment remains effectively nonexistent in practice. From a network-administration perspective, the protocol’s use of port 443 substantially impedes transparent DNS policy enforcement, as DoH traffic cannot be intercepted or redirected by network-level DNS policies without breaking the TLS session—a design trade-off that positions privacy above administrative observability.
DoT - DNS-over-TLS
DNS-over-TLS (DoT), defined in RFC 7858 (2016), wraps the standard DNS wire-format protocol within a TLS session established on the dedicated TCP port 853, providing transport-layer encryption and mutual authentication between DNS clients and their configured Caching Name Server. Unlike DoH, DoT operates on a distinct, well-known port, making it readily identifiable and selectively blockable at the network perimeter—a characteristic regarded as advantageous in enterprise environments where transparent DNS policy enforcement is operationally required.
DoT is applicable to client-to-CNS communication and can additionally be employed for CNS-to-ANS recursive resolution traffic, theoretically providing end-to-end encryption of the full resolution path; however, this deployment scenario remains rare in practice owing to the absence of universal ANS-side DoT support and the lack of a standardized mechanism by which resolvers can discover and authenticate upstream authoritative servers via TLS without manual configuration.
Additional DNS Protocols
mDNS - Multicast DNS
Multicast DNS (mDNS), standardized in RFC 6762 (2013) following earlier experimental deployments as Apple’s Bonjour and the Zeroconf initiative, enables DNS-like name resolution within a link-local scope without the requirement of a dedicated DNS server infrastructure. Participating nodes transmit and receive DNS messages over the well-known multicast addresses 224.0.0.251 (IPv4) and FF02::FB (IPv6) on UDP port 5353, supporting zero-configuration service discovery on LAN segments through fully decentralized peer-to-peer exchange.
mDNS is not applicable to Authoritative or Caching Name Server roles in the conventional sense; its operational scope is explicitly confined to the link-local domain, precluding any path to global Internet name resolution. From a security standpoint, the absence of authentication mechanisms in mDNS renders it susceptible to mDNS poisoning attacks analogous to classical ARP spoofing—a malicious node may respond to mDNS queries with forged resource records, redirecting traffic to attacker-controlled services—making mDNS an inappropriate protocol for security-sensitive resolution tasks beyond trusted LAN boundaries.
LLMNR - Link-Local Multicast Name Resolution
Link-Local Multicast Name Resolution (LLMNR), specified in RFC 4795 (2007), provides a fallback name-resolution mechanism for link-local segments in environments where a conventional DNS server is unavailable, and is predominantly implemented by Microsoft Windows operating systems as part of the NetBIOS successor architecture. LLMNR queries are transmitted as multicast messages on 224.0.0.252 (IPv4) and FF02::1:3 (IPv6) over UDP and TCP port 5355, with responding nodes replying via unicast to the originating querier.
LLMNR is not applicable to ANS or CNS roles in conventional DNS infrastructure; it functions strictly as a last-resort peer resolution mechanism scoped to the link-local segment. From a security perspective, LLMNR is widely regarded as hazardous: the protocol’s complete absence of authentication allows tools such as Responder to intercept any unanswered LLMNR query and reply with a forged response, redirecting the victim’s connection to an attacker-controlled host and enabling NTLM credential hash capture. Disabling LLMNR through Group Policy is consequently a standard hardening recommendation in enterprise security frameworks, including CIS Benchmarks and DISA STIGs.
The DNS Implementation Chaos
Modern Linux systems exemplify the DNS configuration nightmare. A typical Ubuntu installation demonstrates the problem perfectly:
Configuration Entities
On a standard Ubuntu system, the following DNS entities are involved.
netplan
- Network configuration abstraction layer
- Can use either NetworkManager or systemd-networkd as renderer
- Adds yet another configuration layer to manage
- YAML-based configuration that ultimately controls lower layers
systemd-resolved
- systemd’s integrated DNS stub resolver
- Provides local caching DNS service on
127.0.0.53 - Hooks into
/etc/resolv.confvia symlink - Supports DNS-over-TLS (DoT) but not universally configured
- Implements multicast DNS (mDNS) and LLMNR for local name resolution
NetworkManager
- NetworkManager controls network interfaces and DNS configuration
- Integrates with multiple DNS resolvers
- Can use either systemd-resolved or dnsmasq as backend
- Manages
/etc/resolv.confsymlinks and redirections
dnsmasq
- Lightweight DNS forwarder and DHCP server
- Often used by NetworkManager as DNS proxy
- Provides local DNS caching
- May conflict with systemd-resolved when both active
nsswitch
/etc/nsswitch.confdefines the system-wide name resolution source order for all processes: typicallyfiles(local/etc/hosts) followed bydns(resolver defined in/etc/resolv.conf) and optionally mDNS- The
dnsNSS plugin resolves names via/etc/resolv.confdirectly through glibc; if that file is not symlinked to systemd-resolved’s stub resolver (127.0.0.53)—for example when overwritten by a DHCP client or manually reconfigured—queries bypass systemd-resolved entirely, rendering any per-interface DoT/DoH policy invisible to the application layer - On systems using systemd-resolved, the
libnss-resolvepackage must be installed and thehosts:line in/etc/nsswitch.confmust replace thednskeyword withresolve(e.g.hosts: files resolve [!UNAVAIL=return] dns)—without this change, glibc will not route name lookups through systemd-resolved and its encrypted-resolver configuration will have no effect
dnscrypt-proxy
- Open-source DNS proxy implementing the DNSCrypt protocol, which authenticates DNS communications using elliptic-curve cryptography (X25519 key agreement, XSalsa20-Poly1305 authenticated encryption) and encrypts query payloads end-to-end between the local client and an upstream DNSCrypt-capable resolver
- Supports DNS-over-HTTPS (DoH) as an alternative encrypted transport, with additional capabilities including query-based filtering, response caching, DNS-based load balancing, and comprehensive query logging, making it a versatile privacy-enhancing layer deployable independently of the underlying operating system DNS stack
The provisioning of DNS resolver addresses via DHCP further compounds this complexity: DHCP-assigned resolvers distributed by gateway appliances or ISP infrastructure implicitly override any locally configured encrypted DNS settings in the majority of operating system implementations, effectively nullifying client-side DNS encryption deployments that are not enforced at or below the DHCP server tier.
Resume
The landscape of encrypted DNS implementations—particularly on the client side—has grown increasingly fragmented: a proliferating set of software products, daemons, and configuration layers each address parts of the problem in isolation, raising overall system complexity rather than reducing it. What is actually desired is a single, unified solution that transparently enforces encrypted DNS across all resolution paths without requiring per-application or per-interface configuration.
The Original Goal: Securing DNS Infrastructure
When DNS security initiatives began gaining traction in the mid-2000s, the objectives were clear and ambitious:
Transport Layer
- Encrypt DNS transport from local network to recursive resolver
- Encrypt DNS transport from recursive resolver to authoritative server(s)
- Eliminate DNS cache poisoning and man-in-the-middle attacks (response rewriting at the network level)
Integrity
- Ensure DNS responses actually come from legitimate authoritative servers
- Prevent DNS cache poisoning attacks (overwrite DNS cache content)
- Guarantee cryptographic integrity of DNS response data from authoritative origin to client (signature validation over response payload, not IP-layer addressing)
Cryptography
- Provide cryptographic proof of answer validity
- Cryptographically sign DNS zones at authoritative servers
- Provide chain of trust from DNS root through TLDs to individual domains
- Enable resolvers to validate response authenticity
- Detect and reject forged or tampered DNS responses
Privacy Layer
- Prevent ISPs and network operators from monitoring/logging queries
- Maintain user privacy regarding browsing habits and service usage
Current Implementation Status: Mixed Results and High Complexity
Despite two decades of standardization efforts, DNS security implementation remains fragmented and incomplete:
DNSSEC Zone Signing
- Root zone signed since 2010
- Most TLDs now DNSSEC-enabled
- Only ~1.5% of .com domains signed (2025 data)
CNS DNSSEC Implementation
- Many resolvers don’t validate DNSSEC signatures
- End-user applications rarely verify DNSSEC status
- DNSSEC configuration is complex for zone administrators unfamiliar with cryptographic concepts
DoT/DoH Adoption
- Major public resolvers support encrypted DNS (Cloudflare, Google, Quad9)
- Not “transparent”, commonly must be enabled in software, not OS
- Operating system support inconsistent (Android 9+, iOS 14+, Linux manual)—only when the operating system itself provides native DoT/DoH
- Browser implementations vary (Firefox yes, Safari partial, Chrome configurable)
- Most home routers don’t support or forward encrypted DNS
ISP Laziness
- ISP-provided resolvers rarely offer encryption
The Integration Problem
While the encryption and integrity protocols described above are individually well-specified, no existing combination delivers a transparent, end-to-end secure resolution path from client through CNS to ANS in a generic, infrastructure-agnostic manner. The author has developed and operated a reference deployment—validated over several years—that uses dnscrypt-proxy (DoH protocol) in conjunction with NextDNS as the upstream CNS resolver, deliberately bypassing any local CNS tier entirely. While this configuration demonstrably improves privacy and integrity on the client-to-CNS segment, it remains a partial solution: the CNS-to-ANS segment is not independently verified at the client, and deployment is not transparent to applications or the operating system. A complete, universally applicable solution remains an open engineering problem.
See also the Hardened Ubuntu with NextDNS article for a practical DoH deployment using dnscrypt-proxy with NextDNS.
Why
- Transparent end-to-end enforcement requires replacing or upgrading every DNS-processing component in the full resolution chain
- Home and SOHO routers: most consumer firmware does not implement DoT or DoH and cannot participate in an encrypted resolution path without replacement or third-party firmware
- ISP recursive resolvers: ISPs rarely offer encrypted DNS endpoints, and their infrastructure remains outside end-user administrative control
- Enterprise network infrastructure: corporate DNS resolvers require coordinated, organisation-wide migration planning
- Application-layer resolvers: browsers, operating systems, and system daemons each maintain independent DNS stacks, all of which must individually be updated or reconfigured
In practice, the principal obstacles are organisational rather than technical: operations teams understandably favour proven stability over protocol migration, engineering teams operate within budgets that rarely include line items for “fix the infrastructure that is technically working”, and stakeholders remain confident that a distributed naming system in continuous production since 1983 must be doing something right—conveniently setting aside the detail that it was never designed to be private. 😉
The Desired Solution
The diagram below illustrates the desired end-to-end encrypted DNS resolution flow, in which every transport segment is protected by TLS and both the CNS and client independently verify cryptographic signatures to ensure response integrity and authenticity.
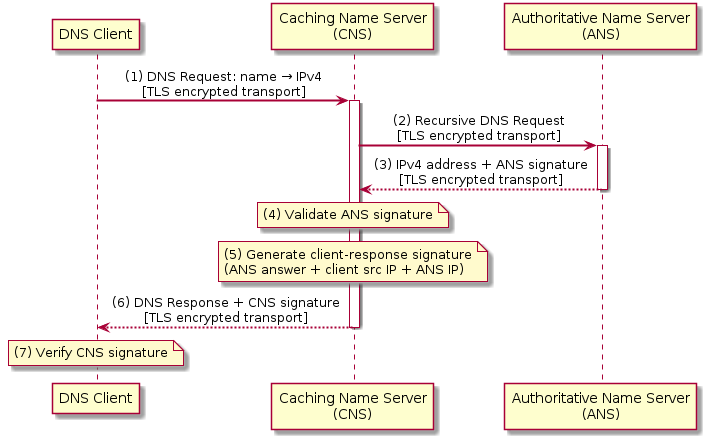
In this model, the client transmits its DNS request to the CNS over an encrypted TLS channel; the CNS forwards a recursive query to the ANS equally over TLS; the ANS returns the resolved IPv4 address together with a cryptographic signature computed over the response payload; the CNS validates the ANS signature, then computes a new signature binding the original client request, the ANS answer, the client source address, and the ANS server address before transmitting the response to the client over TLS; and the client concludes the exchange by verifying the CNS signature, thereby achieving end-to-end cryptographic accountability across the full resolution path. PKCS#11 hardware tokens and HSM integration can be incorporated at both the CNS and ANS tiers to anchor private key material in tamper-resistant hardware, substantially raising the bar for key compromise.
 Remark on DNSSEC runtime verification complexity: The standard DNSSEC specification mandates real-time recursive root-of-trust verification on every resolution—each resolver must chase the chain of trust from the IANA root zone down through TLD and zone delegation at query time. This runtime overhead adds latency, implementation complexity, and operational fragility. Drawing an analogy with X.509 PKI, where recursive root verification is optional and relying parties may configure a trusted intermediate CA as their explicit trust anchor, an equivalent simplification is viable for DNS: anchoring trust at the root CA signing level (IANA root key) and the intermediate CA (zone signing key) is cryptographically sufficient to guarantee zone-data authenticity and integrity. Omitting the per-query recursive chase—while retaining periodic out-of-band key-roll validation—would substantially simplify the protocol, reduce resolver latency, and lower the barrier to correct implementation without meaningfully weakening the security guarantees of the signing hierarchy.
Remark on DNSSEC runtime verification complexity: The standard DNSSEC specification mandates real-time recursive root-of-trust verification on every resolution—each resolver must chase the chain of trust from the IANA root zone down through TLD and zone delegation at query time. This runtime overhead adds latency, implementation complexity, and operational fragility. Drawing an analogy with X.509 PKI, where recursive root verification is optional and relying parties may configure a trusted intermediate CA as their explicit trust anchor, an equivalent simplification is viable for DNS: anchoring trust at the root CA signing level (IANA root key) and the intermediate CA (zone signing key) is cryptographically sufficient to guarantee zone-data authenticity and integrity. Omitting the per-query recursive chase—while retaining periodic out-of-band key-roll validation—would substantially simplify the protocol, reduce resolver latency, and lower the barrier to correct implementation without meaningfully weakening the security guarantees of the signing hierarchy.